2011: expect more of using social media for hacktivism
2011 will be the year of using old attack vectors in new web 2.0 ways. DDoS with social media? Browser-only …
.focus on your core business.
Increasingly, we are hearing in the news about cryptocurrencies like bitcoin, ethereum and dogecoin. A new facet of the conversation, …
… progress will only occur and accelerate if we facilitate the interaction between technologist and entrepreneur – and do it locally.

The deadline for meeting stage 2 standards of meaningful use of EHRs has been delayed until 2014 to encourage more physicians to participate.

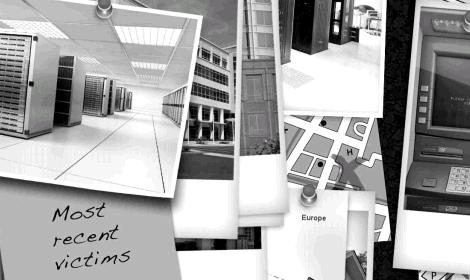
An InfoWorld article summarizes the Verizon 2011 Data Breach Investigations Report(DBIR) and shows that – surprise! – the attackers are …
2011 will be the year of using old attack vectors in new web 2.0 ways. DDoS with social media? Browser-only …
Interesting list of top 20 passwords in the Gawker dump. Hope you aren’t registered on any lifehacker/gawker sites!! http://ow.ly/3pUGl
We provide solutions that secure your data and infrastructure using multiple layers of industry standard tools.
The Economics of Cybercrime and the Law of Malware Probability. Great stats on underground malware economics. http://ow.ly/3ovhu
RT @itsecnews: Infosecurity (US): Senate bill would require minimum cybersecurity standards for internet … http://bit.ly/hV3P15
Latest Stuxnet variant evermore capable. Ecrypted bot communication makes it near impossible to analyse how it’s working. http://ow.ly/3nfhC
New malware encrypts your files and demands cash to decrypt them. Recommendation: encrypt your kids before they can! http://ow.ly/3m7r9
Didn’t know image, audio & video files were this exploitable. Check out “Malware goes to the movies”: http://ow.ly/3ljNj Kudos @ayampolskiy
Day-in-the-life of a bankbot. I rec’d the email this article refers to. I wonder who in my 7 degrees is …
Domain Name Service providers back slowly away from WikiLeaks. http://ow.ly/3jOGV Peer-to-peer DNS forthcoming. http://ow.ly/3jOL5 Weird!!