SecurID Suffers Data Security Breach
RSA, one of the pioneering companies of information security and the creator of SecurID technology in use by thousands of …
.focus on your core business.
Increasingly, we are hearing in the news about cryptocurrencies like bitcoin, ethereum and dogecoin. A new facet of the conversation, …
… progress will only occur and accelerate if we facilitate the interaction between technologist and entrepreneur – and do it locally.

The deadline for meeting stage 2 standards of meaningful use of EHRs has been delayed until 2014 to encourage more physicians to participate.

An InfoWorld article summarizes the Verizon 2011 Data Breach Investigations Report(DBIR) and shows that – surprise! – the attackers are …
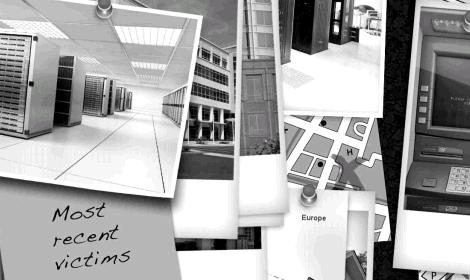
RSA, one of the pioneering companies of information security and the creator of SecurID technology in use by thousands of …
Most other chat protocols/services do not use TLS/SSL or it’s optional and off by default, and thus it’s a low-hanging vector for data breach and leakage.
For as little as $100, equipment can be obtained off-the-shelf and configured to sniff the codes used by these automobile systems.
The only true defense is behavior: not clicking, not opening, etc.
In the words of some great football coach, your best offense is a solid defense. And so it goes with computer systems security…
By ‘utility’ we mean you get all the benefits of the service, without investing in and maintaining the infrastructure.
From Hacktivists to ‘the Professionals’, DDoS attacks are a major tool. http://ow.ly/3sKj2 And detailed DDoS discussion: http://ow.ly/3sKhs
2011 will be the year of using old attack vectors in new web 2.0 ways. DDoS with social media? Browser-only …
Interesting list of top 20 passwords in the Gawker dump. Hope you aren’t registered on any lifehacker/gawker sites!! http://ow.ly/3pUGl
We provide solutions that secure your data and infrastructure using multiple layers of industry standard tools.